Well, the question was clearly for someone else. (I guess it’s easy to miss that a reply was addressed to some particular post, even though the forum shows the information.)
I read @Bendys answer, but did not notice it is question for me. Yes, I am using Sentinel.
Rollback to previous snapshot
252 | pre | 2019-02-06 23:50:35 +0100 | Automatic pre-update snapshot
pkgupdate ok
root@Turris_Omnia:~# pkgupdate
WARN:Script file:///usr/share/updater/localrepo/localrepo.lua not found, but ignoring its absence as requested
WARN:Requested package luci-i18n-ddns-en that is missing, ignoring as requested.
INFO:Queue install of updater-ng/turris/60.4.7-3.6-1
Following updater runs finished without a problem - it makes sense, that error was in postrm script… Well, majordomo somehow still remained installed from the former times and nothing forced me to remove it… but maybe I’ll do it now…
Regarding the backtraces - yes, I faced some problems with my ISP (Vodafone CZ VDSL). First, they moved me behind an IPv4 NAT, so my 6to4 interface stopped working (and it got into a quite fast “re-up” loop, so I disabled IPv6 in Foris for now). Tonight, the IPv4 connection was quite flaky, I got again several of these netifd traces and TO restarted several times (probably due to these traces). But still, WAN connection glitches shouldn’t make the kernel segfault or the router restart, or should they? And do you know why it mostly segfaults on page allocations? I usually have like 0.5 GB free RAM…
The likely culprit is the outdated netifd in TOS3.x, which probably will not get fixed any more in TOS3.x branch but only TOS4.x. I had similar issues with ipv6 on the wan and had to disable it too..
Since your connection is PPPoE and thus require kernel-modules the seqfault could be very well related.
Changelog of Turris OS 3.11.3 RC4
Package updates:
- updater-ng: fix for localrepo (mentioned here)
- foris-controller-openvpn-module: compression logic updates (Gitlab issue)
- kernel: update
Security updates:
- openssh: update to version 7.9p1-1 (fixes CVE-2019-6109, CVE-2019-6111)
- unbound: add patches for OpenSSL 1.0.2 host verify fix from Unbound
- tiff: fix for CVE-2019-6128
update from RC3 to RC4 went ok. unbound patch seems to be working. no issues thus far in the logs
just update to RC4 2x omnia routers, working without any issues
16:09:34 err modprobe[]: failed to open /lib/modules/4.4.172-7bc33afbb1b35f5830b2b1b42c9cd8a0-0/blocklayoutdriver.ko
Are these okay during the update?
just updated to RC4 on my omnia, no issues.
Yes, the newest RC also runs well on my Omnia.
For me, UPnP still doesn’t working  I don’t know if ISP can block this feature or if it is bug in Windows 10 Pro x64 1809, but still I see “no active redirections”. My uTrorrent is set correctly, service is enabled and started. I don’t know
I don’t know if ISP can block this feature or if it is bug in Windows 10 Pro x64 1809, but still I see “no active redirections”. My uTrorrent is set correctly, service is enabled and started. I don’t know 
The part around your ISP is about your router (its WAN) getting a public IPv4. Well, theoretically they might specifically block torrents, as I’ve heard such ideas from ISPs already but they don’t seem too common nowadays.
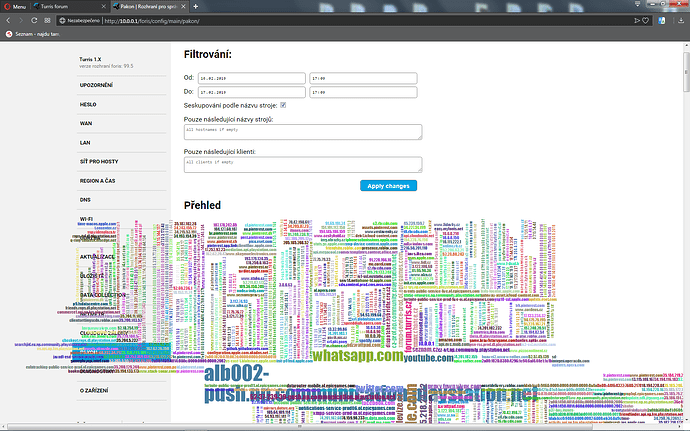
I tested all high ports from 1024 to 65535 TCP and UDP and all are closed.  Is possible that my issue is in Knot resolver on my Turris 1.x? Maybe I see problem, where it isn’t.
Is possible that my issue is in Knot resolver on my Turris 1.x? Maybe I see problem, where it isn’t.
I can’t see how DNS would be related. There’s still no knot-resolver package for Turris 1.x, too. (Unbound is the default resolver in there.)
So i really don’t know. I also tried WiFi connection directly to router to bypass switch, but without effect.
Did you see UPnP server not running? ?
I tried both commands, without effect 
OpenVPN plugin still doesn’t work: