Hello! Please help with routing - I have a Turris Omnia (OS version: 3.8.5), trying to build OpenVPN tunnel. So the steps I’ve made: OPENVPN->Server configuration: Configuration enabled=true, OpenVPN network=192.168.3.0/24, all traffic through vpn=false, Use DNS from vpn=false This is config:
config openvpn 'server_turris’
option enabled '1’
option port '1194’
option proto 'udp’
option dev 'tun_turris’
option ca '/etc/ssl/ca/openvpn/ca.crt’
option crl_verify '/etc/ssl/ca/openvpn/ca.crl’
option cert '/etc/ssl/ca/openvpn/01.crt’
option key '/etc/ssl/ca/openvpn/01.key’
option dh '/etc/dhparam/dh-default.pem’
option server '192.168.3.0 255.255.255.0’
option ifconfig_pool_persist '/tmp/ipp.txt’
option duplicate_cn '0’
option keepalive '10 120’
option comp_lzo 'yes’
option persist_key '1’
option persist_tun '1’
option status '/tmp/openvpn-status.log’
option verb '3’
option mute '20’
list push ‘route 192.168.1.0 255.255.255.0’
Then I started to create OpenVPN client (Ubuntu 16.04). This is virtual machine with 2 network interfaces, wan & lan (gateway). LAN is 192.168.5.0/24, wan is a real IP. I’ve created client config using Turris web-interface. So config looks like:
client
dev tun_turris
proto udp
remote Turris_real_IP 1194
resolv-retry infinite
nobind
persist-key
persist-tun
mute-replay-warnings
-----BEGIN CERTIFICATE-----
-----END CERTIFICATE-----
Certificate:
-----BEGIN CERTIFICATE-----
-----END CERTIFICATE-----
-----BEGIN PRIVATE KEY-----
-----END PRIVATE KEY-----
remote-cert-tls server
comp-lzo
verb 3
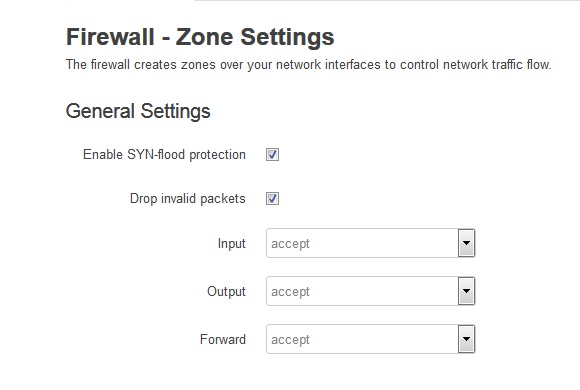
Tunnel is OK, I see tun-interfaces on Turris and on my virtual client. But no ping between machines behind client and server. For example, 192.168.5.5->OpenVPN client<–>Turris server->192.168.1.75. So I’m trying to ping from 192.168.5.5 to 192.168.1.75 - 100% packet loss. All the same in reverse direction - no ping. How to fix it? Thank you.