Dear Turris users,
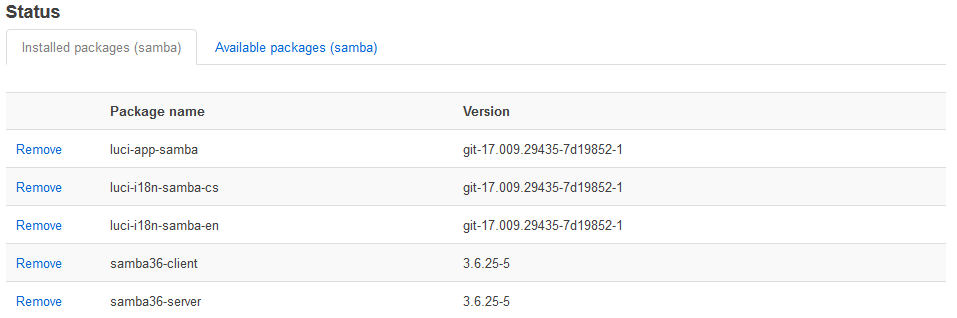
the new security issue has been discovered in samba packages from version 3.5 onwards. This issue allows the attacker to run the malicious code of his choice on the vulnerable device.
We are testing the security patch for Turris routers right now and we want to release it tomorrow.
Until that, samba users can use this workaround:
Add the parameter:
nt pipe support = no
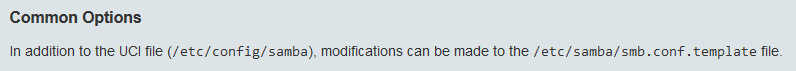
to the [global] section of your smb.conf and restart smbd. This
prevents clients from accessing any named pipe endpoints. Note this
can disable some expected functionality for Windows clients.
Good to know:
- Please, do not open smb sharing to the Internet. Never. It is not secure.
- Keep automatic updates on.
You can find out more about this issue on following links:
Official info from Samba
Article about the issue on Arstechnica
short mention on root.cz for Czech users
Thank you for staying secure with us,
Václav
your Community Manager