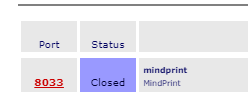
8033 is not for outgoing connections.
Lets first find the minipot process
root@turris:~# ps ax|grep sentinel
3249 ? Sl 1:52 python3 /usr/bin/sentinel-dynfw-client --ipset turris-sn-dynfw-block --cert /var/run/dynfw_server.pub --renew
5872 ? Sl 0:39 sentinel-proxy
5977 ? Sl 0:21 /usr/bin/sentinel-fwlogs --nflog-group=1914
6031 ? Sl 0:01 /usr/bin/sentinel-minipot --ftp=2133 --http=8033 --smtp=5873 --telnet=2333
6054 ? S 0:00 /usr/bin/sentinel-minipot --ftp=2133 --http=8033 --smtp=5873 --telnet=2333
6055 ? S 0:00 /usr/bin/sentinel-minipot --ftp=2133 --http=8033 --smtp=5873 --telnet=2333
6056 ? S 0:00 /usr/bin/sentinel-minipot --ftp=2133 --http=8033 --smtp=5873 --telnet=2333
6057 ? S 0:00 /usr/bin/sentinel-minipot --ftp=2133 --http=8033 --smtp=5873 --telnet=2333
From above we see that Minipot processes started to listen on 4 ports, ftp=2133, http=8033, smtp=5873, telnet=2333, and HaaS SSH honeypot listens on 2525 (these ports opened only for internal, closed to the wan).
Proof
Sentinel:
root@turris:~# netstat -atp|grep sent
tcp 0 0 89.XX.XX.XX:49868 sentinel.turris.cz:7087 ESTABLISHED 3249/python3
tcp 0 0 89.XX.XX.XX:49714 sentinel.turris.cz:1883 ESTABLISHED 5872/sentinel-proxy
tcp 0 0 :::5873 :::* LISTEN 6056/sentinel-minip
tcp 0 0 :::2133 :::* LISTEN 6054/sentinel-minip
tcp 0 0 :::2333 :::* LISTEN 6057/sentinel-minip
tcp 0 0 :::8033 :::* LISTEN 6055/sentinel-minip
From above the first 2 are the outgoing, and other 4 are the locally listening ones.
HaaS:
root@turris:~# netstat -nat|grep 2525
tcp 0 0 0.0.0.0:2525 0.0.0.0:* LISTEN
Now lets look at the firewall
root@turris:~# iptables -t nat -S|grep sentinel
-A zone_wan_prerouting -p tcp -m tcp --dport 22 -m comment --comment "!sentinel: HaaS proxy port redirect" -j REDIRECT --to-ports 2525
-A zone_wan_prerouting -p tcp -m tcp --dport 21 -m comment --comment "!sentinel: Minipot FTP port redirect" -j REDIRECT --to-ports 2133
-A zone_wan_prerouting -p tcp -m tcp --dport 80 -m comment --comment "!sentinel: Minipot HTTP port redirect" -j REDIRECT --to-ports 8033
-A zone_wan_prerouting -p tcp -m tcp --dport 25 -m comment --comment "!sentinel: Minipot SMTP port redirect" -j REDIRECT --to-ports 5873
-A zone_wan_prerouting -p tcp -m tcp --dport 587 -m comment --comment "!sentinel: Minipot SMTP submission port redirect" -j REDIRECT --to-ports 5873
-A zone_wan_prerouting -p tcp -m tcp --dport 23 -m comment --comment "!sentinel: Minipot Telnet port redirect" -j REDIRECT --to-ports 2333
So we see ports 21,22,23,25,80 allowed from the wan.
Rules above mean incoming connections from wan to these ports redirected to internal local listening ports which I wrote above:
21 to 2133,
80 to 8033,
25 to 5873,
23 to 2333,
22 to 2525
So 8033 is the local port for incoming http=80, that means any http connection attempt or attack is redirected to the port 8033, kernel log is correct.
EDIT:
Design of minipot/haas services OK, my initial concern was if the current firewall(syn-flood enabled) and kernel params were enough to survive these attacks, or if we can improve it even more?