I’m also having issues resolving local hostnames; I’ve taken a look at the links above but they don’t address my issue.
(To avoid off-topic discussion, I’m using home.arpa. as my TLD because RFC 8375 explicitly creates home.arpa. for this purpose and RFC 6762 explicitly discourages the use of .local. as a private TLD.)
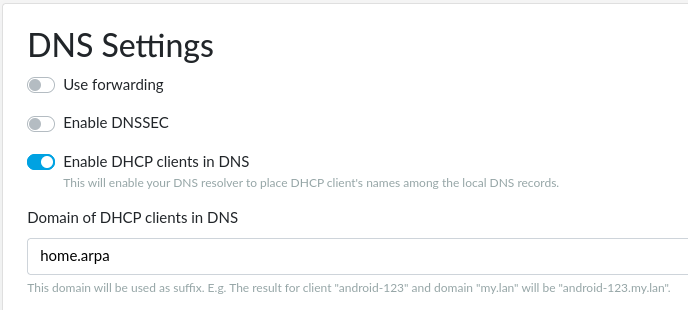
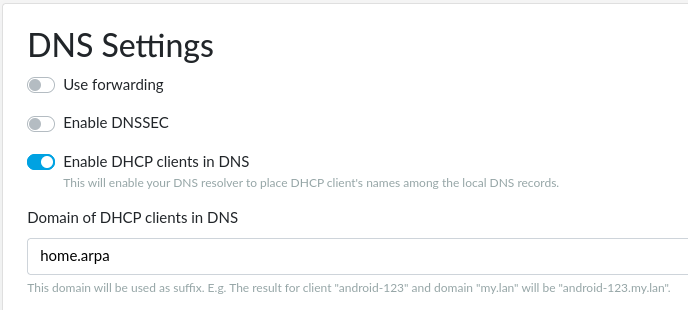
reForis config:
/etc/config/resolver:
config resolver 'kresd'
option rundir '/tmp/kresd'
option log_stderr '1'
option log_stdout '1'
option keep_cache '1'
list rpz_file '/etc/kresd/adb_list.overall'
list hostname_config '/tmp/testhosts'
/tmp/kresd.config:
modules = {
'hints > iterate'
, 'policy'
, 'stats'
, predict = { window = 0, period = 0 }
}
hints.use_nodata(true)
policy.add(policy.rpz(policy.DENY, '/etc/kresd/adb_list.overall'))
hints.config('/tmp/kresd/hints.tmp')
net.listen('0.0.0.0', 53, { kind = 'dns' })
net.listen('0.0.0.0', 853, { kind = 'tls' })
net.listen('::', 53, { kind = 'dns' })
net.listen('::', 853, { kind = 'tls' })
trust_anchors.remove('.')
net.bufsize(1232)
net.ipv4=true
net.ipv6=false
cache.open(20*MB)
user('kresd','kresd')
/tmp/kresd/hints.tmp:
1.2.3.4 testhost.example.dev
192.168.254.250 vmhost.home.arpa
192.168.254.251 vmadmin.home.arpa
192.168.254.101 gitea.home.arpa
Looking up the test host works fine:
; <<>> DiG 9.18.12-0ubuntu0.22.04.1-Ubuntu <<>> testhost.example.dev
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 44671
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1
;; ANSWER SECTION:
testhost.example.dev. 5 IN A 1.2.3.4
However, looking up my actual hosts does not:
; <<>> DiG 9.18.12-0ubuntu0.22.04.1-Ubuntu <<>> gitea.home.arpa
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NXDOMAIN, id: 35765
;; flags: qr rd ra; QUERY: 1, ANSWER: 0, AUTHORITY: 1, ADDITIONAL: 2
;; AUTHORITY SECTION:
gitea.home.arpa. 10800 IN SOA gitea.home.arpa. nobody.invalid. 1 3600 1200 604800 10800
;; ADDITIONAL SECTION:
explanation.invalid. 10800 IN TXT "Blocking is mandated by standards, see references on https://www.iana.org/assignments/locally-served-dns-zones/locally-served-dns-zones.xhtml"
I’m running TOS 6.3.2, kernel 5.15.96, kresd 5.6.0