I seem to have an IPv6 firewalling problem : IPv6 originating on the TO does not receive answers. I get this when using an IPv6 DNS as forwarder, I see the DNS requests going out, I see the answers being sent by the DNS server, but the answer is not seen by the TO
Same thing with a ping (ICMP)
For outgoing SSH, the server does not receive the SYN packets.
I dp not see how to allow the turris outgoing statefull IPv6 connections to the WAN zone. DOes someone have any help ?
I believe TO would not be blocking this, at least not in close-to-default setting.
That’s what I believed, but the result is there. I did only basic configuration of FW through Luci
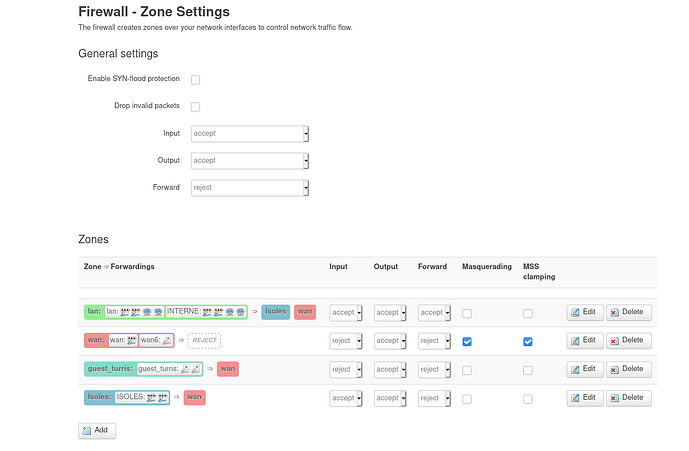
Here is the setting, But I do not see to which zone the TO itself belongs
By default this should be considered as a lan => wan but you screenshot show you have defined custom zone (ISOLES, INTERNE).
Yes I have several zones on the inside side that I want to separate, that’s the main reason for me to have my own router.
So How should I do this ?
It works for me:
root@turris:~# ping6 www.ietf.org
PING www.ietf.org(2606:4700:10::6814:6e06) 56 data bytes
64 bytes from 2606:4700:10::6814:6e06: icmp_seq=1 ttl=58 time=1.91 ms
64 bytes from 2606:4700:10::6814:6e06: icmp_seq=2 ttl=58 time=2.42 ms
64 bytes from 2606:4700:10::6814:6e06: icmp_seq=3 ttl=58 time=2.36 ms
^C
--- www.ietf.org ping statistics ---
3 packets transmitted, 3 received, 0% packet loss, time 2003ms
rtt min/avg/max/mdev = 1.915/2.236/2.428/0.235 ms
My setup is very close from the default: just “lan”, “wan”, and “freebox” zone.
For this setup using a TO is useless : the box does it itself.
A solution for me would be to disable all FW configuration done through Luci, Foris or UCI and I do it myself directly with iptables and ip6tables.
Is it possible ?
Found the problem : the IP I used on turris was the same the uplink router used…
This topic was automatically closed 3 days after the last reply. New replies are no longer allowed.