Hi Team
I finally have some time to get back to this.
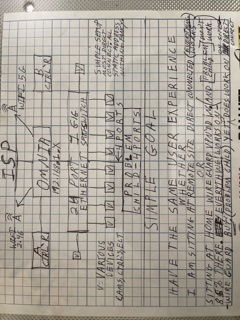
My problem is simple. I can’t get devices 192.168.1. " 121 and 122 and 123 and 124" to work over WG VPN. They should work. No obvious reason they not working, now that I am showing up on the OMNIA with the same subnet they are on.
Simply, they should be working. EVERYTHING else I have hanging of my OMNIA works over WG VPN! Everything else!
I really really want to use these devices remotely and something is stopping me. I just can’t see it. If I am up at the remote site and plugged in on Ethernet or WIFI’ing it they work. What is WG VPN doing to, or lacking in, or changing what part of the environment to kill them, on OMNIA or Laptop or both at same time, is the question?
I just want to get them them fixed & working on VPN.
Here is your requested info below, hope I did it right.
8888888888888888888888888888888888888888888888888888888888888888888
root@turris:/etc/config# cat network
config interface ‘loopback’
option ifname ‘lo’
option proto ‘static’
option ipaddr ‘127.0.0.1’
option netmask ‘255.0.0.0’
config globals ‘globals’
option ula_prefix ‘fd7c:de15:260e::/48’
config interface ‘lan’
option type ‘bridge’
option proto ‘static’
option ipaddr ‘192.168.1.1’
option netmask ‘255.255.255.0’
option ip6assign ‘60’
option bridge_empty ‘1’
option ifname ‘lan0 lan1 lan2 lan3 lan4’
config interface ‘wan’
option ifname ‘eth2’
option proto ‘dhcp’
option ipv6 ‘0’
config interface ‘guest_turris’
option enabled ‘1’
option type ‘bridge’
option proto ‘static’
option ipaddr ‘10.111.222.1’
option netmask ‘255.255.255.0’
option bridge_empty ‘1’
config interface ‘wan6’
option ifname ‘@wan’
option proto ‘none’
config interface ‘wg0’
option proto ‘wireguard’
option private_key ‘REDACTED’
option listen_port ‘51820’
list addresses ‘10.0.0.1/24’
list addresses ‘10.111.222.1/24’
config interface ‘wg1’
option proto ‘wireguard’
option listen_port ‘51821’
option private_key ‘REDACTED’
list addresses ‘192.168.1.253/30’
config wireguard_wg0
option public_key ‘REDACTED’
option description ‘Phone’
option preshared_key ‘REDACTED’
option route_allowed_ips ‘1’
option persistent_keepalive ‘25’
list allowed_ips ‘10.0.0.2’
list allowed_ips ‘192.168.1.1/24’
list allowed_ips ‘10.111.222.1/24’
config wireguard_wg1
option public_key ‘REDACTED’
option description ‘Laptop’
option preshared_key ‘REDACTED’
option route_allowed_ips ‘1’
option persistent_keepalive ‘25’
option endpoint_port ‘51821’
list allowed_ips ‘192.168.1.1/24’
list allowed_ips ‘10.111.222.1/24’
88888888888888888888888888888888888888888888888888888888888888888888
laptop routing table
111111111111111111111111111111111111111111111111111111111111111111111111111111
C:>netstat -r -a
Interface List
19…WireGuard Tunnel #2
12…c4 46 19 6f 91 bb …Broadcom 802.11n Network Adapter
11…a4 ba db d8 34 21 …Realtek PCIe GBE Family Controller
1…Software Loopback Interface 1
18…00 00 00 00 00 00 00 e0 Microsoft ISATAP Adapter
20…00 00 00 00 00 00 00 e0 Microsoft ISATAP Adapter #2
222222222222222222222222222222222222222222222222222222
IPv4 Route Table
333333333333333333333333333333333333333333333333333333
Active Routes:
Network Destination Netmask Gateway Interface Metric
0.0.0.0 0.0.0.0 172.20.10.1 172.20.10.2 25
0.0.0.0 128.0.0.0 On-link 192.168.1.254 5
127.0.0.0 255.0.0.0 On-link 127.0.0.1 306
127.0.0.1 255.255.255.255 On-link 127.0.0.1 306
127.255.255.255 255.255.255.255 On-link 127.0.0.1 306
127.255.255.255 255.255.255.255 On-link 192.168.1.254 261
128.0.0.0 128.0.0.0 On-link 192.168.1.254 5
172.20.10.0 255.255.255.240 On-link 172.20.10.2 281
172.20.10.2 255.255.255.255 On-link 172.20.10.2 281
172.20.10.15 255.255.255.255 On-link 172.20.10.2 281
192.168.1.254 255.255.255.255 On-link 192.168.1.254 261
224.0.0.0 240.0.0.0 On-link 127.0.0.1 306
224.0.0.0 240.0.0.0 On-link 172.20.10.2 281
255.255.255.255 255.255.255.255 On-link 127.0.0.1 306
255.255.255.255 255.255.255.255 On-link 172.20.10.2 281
44444444444444444444444444444444444444444444444444444444444444444
Persistent Routes:
None
IPv6 Route Table
55555555555555555555555555555555555555555555555555555555555555555
Active Routes:
If Metric Network Destination Gateway
1 306 ::1/128 On-link
1 306 ff00::/8 On-link
66666666666666666666666666666666666666666666666666666666666666666
Persistent Routes:
None
77777777777777777777777777777777777777777777777777777777777777777
tracert
C:>tracert -h 5 192.168.1.121
Tracing route to 192.168.1.121 over a maximum of 5 hops
1 103 ms 82 ms 79 ms 192.168.1.253
2 * * * Request timed out.
3 * * * Request timed out.
4 * * * Request timed out.
5 * * * Request timed out.
Trace complete.
C:>tracert -h 5 192.168.1.124
Tracing route to 192.168.1.124 over a maximum of 5 hops
1 90 ms 131 ms 120 ms 192.168.1.253
2 * * * Request timed out.
3 * * * Request timed out.
4 * * * Request timed out.
5 * * * Request timed out.
Trace complete.
C:>tracert -h 5 192.168.1.120
Tracing route to 192.168.1.120 over a maximum of 5 hops
1 147 ms 114 ms 111 ms 192.168.1.253
2 * * * Request timed out.
3 135 ms 120 ms 118 ms 192.168.1.120
Trace complete.
88888888888888888888 End of your requested info 888888888888888888888
88888888 Add on info that I am including. Disregard if not useful 888888888888
C:>ping 192.168.1.121
Pinging 192.168.1.121 with 32 bytes of data:
Request timed out.
Request timed out.
Request timed out.
Request timed out.
Ping statistics for 192.168.1.121:
Packets: Sent = 4, Received = 0, Lost = 4 (100% loss),
C:>ping 192.168.1.124
Pinging 192.168.1.124 with 32 bytes of data:
Request timed out.
Request timed out.
Request timed out.
Request timed out.
Ping statistics for 192.168.1.124:
Packets: Sent = 4, Received = 0, Lost = 4 (100% loss),
C:>
C:>ping 192.168.1.120
Pinging 192.168.1.120 with 32 bytes of data:
Reply from 192.168.1.120: bytes=32 time=117ms TTL=12
Reply from 192.168.1.120: bytes=32 time=108ms TTL=12
Reply from 192.168.1.120: bytes=32 time=143ms TTL=12
Reply from 192.168.1.120: bytes=32 time=91ms TTL=126
Ping statistics for 192.168.1.120:
Packets: Sent = 4, Received = 4, Lost = 0 (0% lo
Approximate round trip times in milli-seconds:
Minimum = 91ms, Maximum = 143ms, Average = 114ms
(I can Ping Every device on my OMNIA if direct connected???)
8888888888888888888888888888888888888888888888888888888888888888888
(SOME LAPTOP PORT INFO THAT MIGHT BE USEFUL.)
C:>NETSTAT -a -b
Active Connections
Proto Local Address Foreign Address State
TCP 0.0.0.0:135 Laptop3-PC:0 LISTENING
RpcSs
[svchost.exe]
TCP 0.0.0.0:445 Laptop3-PC:0 LISTENING
Can not obtain ownership information
TCP 0.0.0.0:554 Laptop3-PC:0 LISTENING
[wmpnetwk.exe]
TCP 0.0.0.0:1025 Laptop3-PC:0 LISTENING
[wininit.exe]
TCP 0.0.0.0:1026 Laptop3-PC:0 LISTENING
eventlog
[svchost.exe]
TCP 0.0.0.0:1027 Laptop3-PC:0 LISTENING
Schedule
[svchost.exe]
TCP 0.0.0.0:1028 Laptop3-PC:0 LISTENING
[hdhomerun_record.exe]
TCP 0.0.0.0:1029 Laptop3-PC:0 LISTENING
[lsass.exe]
TCP 0.0.0.0:1030 Laptop3-PC:0 LISTENING
[services.exe]
TCP 0.0.0.0:2869 Laptop3-PC:0 LISTENING
Can not obtain ownership information
TCP 0.0.0.0:10243 Laptop3-PC:0 LISTENING
Can not obtain ownership information
TCP 172.20.10.2:139 Laptop3-PC:0 LISTENING
Can not obtain ownership information
TCP 192.168.1.254:139 Laptop3-PC:0 LISTENING
Can not obtain ownership information
TCP 192.168.1.254:7439 192.168.1.1:http CLOSE_WAIT
[msedge.exe]
TCP 192.168.1.254:7783 192.168.1.1:http CLOSE_WAIT
[msedge.exe]
TCP 192.168.1.254:22059 192.168.1.1:http CLOSE_WAIT
[msedge.exe]
TCP 192.168.1.254:23231 192.168.1.1:http CLOSE_WAIT
[msedge.exe]
TCP 192.168.1.254:33328 li927-71:8003 ESTABLISHED
[hdhomerun_record.exe]
TCP 192.168.1.254:36789 192.168.1.1:ssh ESTABLISHED
[putty.exe]
TCP 192.168.1.254:47597 192.168.1.1:http CLOSE_WAIT
[msedge.exe]
TCP 192.168.1.254:61548 192.168.1.1:http CLOSE_WAIT
[msedge.exe]
TCP [::]:135 Laptop3-PC:0 LISTENING
RpcSs
[svchost.exe]
TCP [::]:445 Laptop3-PC:0 LISTENING
Can not obtain ownership information
TCP [::]:554 Laptop3-PC:0 LISTENING
[wmpnetwk.exe]
TCP [::]:1025 Laptop3-PC:0 LISTENING
[wininit.exe]
TCP [::]:1026 Laptop3-PC:0 LISTENING
eventlog
[svchost.exe]
TCP [::]:1027 Laptop3-PC:0 LISTENING
Schedule
[svchost.exe]
TCP [::]:1029 Laptop3-PC:0 LISTENING
[lsass.exe]
TCP [::]:1030 Laptop3-PC:0 LISTENING
[services.exe]
TCP [::]:2869 Laptop3-PC:0 LISTENING
Can not obtain ownership information
TCP [::]:10243 Laptop3-PC:0 LISTENING
Can not obtain ownership information
UDP 0.0.0.0:500 :
IKEEXT
[svchost.exe]
UDP 0.0.0.0:4500 :
IKEEXT
[svchost.exe]
UDP 0.0.0.0:5004 :
[wmpnetwk.exe]
UDP 0.0.0.0:5005 :
[wmpnetwk.exe]
UDP 0.0.0.0:5353 :
[msedge.exe]
UDP 0.0.0.0:5353 :
[msedge.exe]
UDP 0.0.0.0:5355 :
Dnscache
[svchost.exe]
UDP 0.0.0.0:49154 :
[hdhomerun_record.exe]
UDP 0.0.0.0:52205 :
[wireguard.exe]
UDP 0.0.0.0:65001 :<<<<< SIGNIFICANT PORT. 4 DEVICES NOT WORKING LISTEN ON 65001 TO BE DISCOVERED.
[hdhomerun_record.exe]
UDP 127.0.0.1:1900 :
SSDPSRV
[svchost.exe]
UDP 127.0.0.1:60991 :
SSDPSRV
[svchost.exe]
UDP 172.20.10.2:137 :
Can not obtain ownership information
UDP 172.20.10.2:138 :
Can not obtain ownership information
UDP 172.20.10.2:1900 :
SSDPSRV
[svchost.exe]
UDP 172.20.10.2:49154 :
[hdhomerun_record.exe]
UDP 172.20.10.2:60990 :
SSDPSRV
[svchost.exe]
UDP 192.168.1.254:137 :
Can not obtain ownership information
UDP 192.168.1.254:138 :
Can not obtain ownership information
UDP 192.168.1.254:1900 :
SSDPSRV
[svchost.exe]
UDP 192.168.1.254:60989 :
SSDPSRV
[svchost.exe]
UDP [::]:500 :
IKEEXT
[svchost.exe]
UDP [::]:4500 :
IKEEXT
[svchost.exe]
UDP [::]:5004 :
[wmpnetwk.exe]
UDP [::]:5005 :
[wmpnetwk.exe]
UDP [::]:5355 :
Dnscache
[svchost.exe]
UDP [::]:52205 :
[wireguard.exe]
UDP [::1]:1900 :
SSDPSRV
[svchost.exe]
UDP [::1]:60988 :
SSDPSRV
[svchost.exe]
888888888888888888888 End of my add on info 88888888888888888888888888
Thanks team