Now that fail2ban is available as openwrt package, it is quite easy to set up an openvpn jail. I did that and I have >200 unique IP addresses per week trying to get in.
Would it be possible to get the jailed addresses to the dynamic firewall?
Now that fail2ban is available as openwrt package, it is quite easy to set up an openvpn jail. I did that and I have >200 unique IP addresses per week trying to get in.
Would it be possible to get the jailed addresses to the dynamic firewall?
For those interested, here’s the config I’m using:
# cat /etc/fail2ban/jail.d/openvpn.conf
# Fail2Ban configuration fragment for OpenVPN
[openvpn]
enabled = true
port = 1194
protocol = udp
filter = openvpn
logpath = /var/log/messages*
maxretry = 3
bantime=604800
findtime=86400
# block the whole /24 subnet of the attacker
banaction = iptables-multiport24subnet
banaction_allports =
# cat /etc/fail2ban/action.d/iptables-multiport24subnet.conf
# Fail2Ban configuration file
#
# Author: Cyril Jaquier
# Modified by Yaroslav Halchenko for multiport banning
# Modified: Martin Pecka
# Blocking whole /24 subnets.
#
[INCLUDES]
before = iptables-common.conf
[Definition]
# Option: actionstart
# Notes.: command executed on demand at the first ban (or at the start of Fail2Ban if actionstart_on_demand is set to false).
# Values: CMD
#
actionstart = <iptables> -N f2b-<name>
<iptables> -A f2b-<name> -j <returntype>
<iptables> -I <chain> -p <protocol> -m multiport --dports <port> -j f2b-<name>
# Option: actionstop
# Notes.: command executed at the stop of jail (or at the end of Fail2Ban)
# Values: CMD
#
actionstop = <iptables> -D <chain> -p <protocol> -m multiport --dports <port> -j f2b-<name>
<actionflush>
<iptables> -X f2b-<name>
# Option: actioncheck
# Notes.: command executed once before each actionban command
# Values: CMD
#
actioncheck = <iptables> -n -L <chain> | grep -q 'f2b-<name>[ \t]'
# Option: actionban
# Notes.: command executed when banning an IP. Take care that the
# command is executed with Fail2Ban user rights.
# Tags: See jail.conf(5) man page
# Values: CMD
#
actionban = <iptables> -I f2b-<name> 1 -s <ip>/24 -j <blocktype>
# Option: actionunban
# Notes.: command executed when unbanning an IP. Take care that the
# command is executed with Fail2Ban user rights.
# Tags: See jail.conf(5) man page
# Values: CMD
#
actionunban = <iptables> -D f2b-<name> -s <ip>/24 -j <blocktype>
[Init]
# cat /etc/fail2ban/filter.d/openvpn.conf
# Fail2Ban filter for selected OpenVPN rejections
#
#
[Definition]
# Example messages (other matched messages not seen in the testing server's logs):
# Fri Sep 23 11:55:36 2016 TLS Error: incoming packet authentication failed from [AF_INET]59.90.146.160:51223
# Thu Aug 25 09:36:02 2016 117.207.115.143:58922 TLS Error: TLS handshake failed
failregex = ^.* TLS Error: incoming packet authentication failed from \[AF_INET\]<HOST>:\d+$
^.* <HOST>:\d+ Connection reset, restarting
^.* <HOST>:\d+ TLS Auth Error
^.* <HOST>:\d+ TLS Error: TLS handshake failed$
^.* <HOST>:\d+ VERIFY ERROR
ignoreregex =
And stats for the last week:
Status for the jail: openvpn
|- Filter
| |- Currently failed: 123
| |- Total failed: 1382
| `- File list: /var/log/messages.1 /var/log/messages.2 /var/log/messages.3 /var/log/messages.4 /var/log/messages.5 /var/log/messages.6 /var/log/messages.7 /var/log/messages
`- Actions
|- Currently banned: 216
|- Total banned: 216
My other router is even more favorite:
Status for the jail: openvpn
|- Filter
| |- Currently failed: 102
| |- Total failed: 67340
| `- File list: /var/log/messages.1 /var/log/messages.2 /var/log/messages.3 /var/log/messages.4 /var/log/messages.5 /var/log/messages.6 /var/log/messages.7 /var/log/messages
`- Actions
|- Currently banned: 653
|- Total banned: 758
@peci1 Does this work with TOS6.0/7.0? I am getting my whole log spammed with guys trying to get in via openvpn.
EDIT: Or most likely some bots.
I use it on 6.1.0 and it works without a glitch. I’ve even noticed that the scanners learn they are not welcome and stop trying - in the beginning, I had like 200+ blocked subnets, and now I only have 50-ish…
I really wonder if CZ.NIC wouldn’t want to implement a Reforis module for this.
ha, i was looking for this simple way , thank you very much!
the only thing i’m missing is to ad a specific IP that will not be banned ( the one i use to log in  ) Any idea where and how to do that? thnxs
) Any idea where and how to do that? thnxs
best, Dikke (nOOb)
edit, rather simple, it is in the HELP.
Works like a charm, current 6042 IP’s banned
I haven’t done that, but I expect fail2ban should have some whitelist… Look into the docs.
Checking the logs here… Andy idea what this can be?
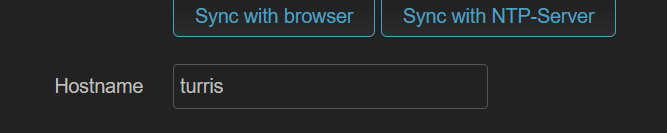
WARNING Unable to find a corresponding IP address for turris: [Errno -2] Name does not resolve
Turris in this case is the name of the router 
Coult it be that you need to use something like turris.lan ?
not sure…i let it run now for 2 weeks or so, to see how it s going. Also not sure if all is working fine, since i do get some fails.
The issue might also be the different timestamps in the syslog.
2023-01-28 10:26:44,037 fail2ban.server [4437]: INFO Starting Fail2ban v0.11.2
2023-01-28 10:26:44,076 fail2ban.observer [4437]: INFO Observer start…
2023-01-28 10:26:44,482 fail2ban.database [4437]: INFO Connected to fail2ban persistent database ‘/sda/fail2ban/fail2ban.sqlite3’
2023-01-28 10:26:44,500 fail2ban.jail [4437]: INFO Creating new jail ‘openvpn’
2023-01-28 10:26:44,726 fail2ban.jail [4437]: INFO Jail ‘openvpn’ uses poller {}
2023-01-28 10:26:44,729 fail2ban.jail [4437]: INFO Initiated ‘polling’ backend
2023-01-28 10:26:45,133 fail2ban.filter [4437]: INFO maxRetry: 3
2023-01-28 10:26:45,198 fail2ban.filter [4437]: INFO findtime: 86400
2023-01-28 10:26:45,200 fail2ban.actions [4437]: INFO banTime: 604800
2023-01-28 10:26:45,202 fail2ban.filter [4437]: INFO encoding: UTF-8
2023-01-28 10:26:45,254 fail2ban.filter [4437]: INFO Added logfile: ‘/var/log/messages’ (pos = 0, hash = 8xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxf)
2023-01-28 10:26:51,644 fail2ban.filter [4437]: WARNING [openvpn] Simulate NOW in operation since found time has too large deviation 1674894411.0 ~ 1674898011.6443248 +/- 60
2023-01-28 10:26:51,645 fail2ban.filter [4437]: WARNING [openvpn] Please check jail has possibly a timezone issue. Line with odd timestamp: Jan 28 09:26:51 turris procd: /etc/rc.d/S99start-indicator: Command failed: Not found
2023-01-28 10:27:10,274 fail2ban.ipdns [4437]: WARNING Unable to find a corresponding IP address for turris: [Errno -3] Try again
2023-01-28 10:27:10,752 fail2ban.actions [4437]: NOTICE [openvpn] Restore Ban 1xx.xxx.xxx.xxx
2023-01-28 10:27:10,935 fail2ban.jail [4437]: INFO Jail ‘openvpn’ started
Status for the jail: openvpn
|- Filter
| |- Currently failed: 3
| |- Total failed: 9
| - File list: /var/log/messages - Actions
|- Currently banned: 994
|- Total banned: 994
`- Banned IP list:
Hmm, I haven’t seen this happening… You can teat the jail with fail2ban-regex /var/log/messages openvpn. That should show you how the parser is working.
this is the result. Sorry, i do not know how to format this correct on the forum. ( by the way, i cloned all your settings, only changed the DB location to ext disc )
Use failregex filter file : openvpn, basedir: /etc/fail2ban
Use log file : /var/log/messages
Use encoding : UTF-8
Failregex: 30 total
|- #) [# of hits] regular expression
| 4) [30] ^.* :\d+ TLS Error: TLS handshake failed$
`-
Ignoreregex: 0 total
Date template hits:
|- [# of hits] date format
| [1616] {^LN-BEG}(?:DAY )?MON Day %k:Minute:Second(?:.Microseconds)?(?: ExYear)?
`-
Lines: 1616 lines, 0 ignored, 30 matched, 1586 missed
[processed in 2.23 sec]
Missed line(s): too many to print. Use --print-all-missed to print all 1586 lines
It seems to be working. Also your above prints told that there actually are banned IPs. The timestamp error as I understand it should be only affecting the startup of F2B when it is loading a database of older banned IPs.
the hostname of the local router is turris, so i think it is looking at that specific name. So, should i change the hostname into something ( in Luci ) fail2ban understands?
Or is this a fail2ban setting?
thx, DIKKE
I just wanted to add that if you are using external storage and log persistency then you could add /srv/log/messages* to logpath = in jail.d
i assume you mean this logpath?
and you suggest ( i use ext storage & log pers. ) to make it :
logpath = in jail.d ?
I think the suggestion was meant to be:
logpath = /srv/log/messages*
in file /etc/fail2ban/jail.d/openvpn.conf
sorry for necrobumping this, just a quick question. Does this still work on Turris OS 7? Since the whole OS os being migrated to nftables…
Version 7 is still on iptables and it still works.